ScalePad Achieves SOC 2 Type II and ISO 27001 Compliance

ScalePad Achieves SOC 2 Type II and ISO 27001 Compliance
Compliance verifies that ScalePad's systems and processes safeguard Partner data.
VANCOUVER, British Columbia, April 24, 2024 (Newswire.com) - ScalePad proudly announces the achievement of SOC 2 Type II and ISO 27001 compliance certifications for its products Lifecycle Manager, Lifecycle Insights, Backup Radar, and ControlMap. This milestone reinforces ScalePad's unwavering dedication to upholding the highest data security, privacy, and integrity standards for its global customer base.
The SOC 2 Type II certification verifies that ScalePad's systems and processes safeguard Partner data against unauthorized access, use, and disclosure. Similarly, the ISO 27001 certification demonstrates ScalePad's commitment to implementing comprehensive information security management systems, encompassing policies, procedures, and controls to manage and protect sensitive information.
"Cybersecurity isn't just a box to check; it's a guiding principle,” said Dan Wensley, CEO of ScalePad. “Achieving SOC 2 Type II and ISO 27001 compliance enforces our commitment to maintaining and continuously improving our security measures. This commitment to rigorous standards demonstrates our dedication to enhancing security practices in response to evolving threats.”
“Elevating security posture while cultivating trust is at the heart of what cybersecurity compliance is all about,” said security compliance expert Dan Fox, who also works as a lead in cybersecurity education for Scalepad’s ControlMap team. “ScalePad's commitment to security and protecting our partner ecosystem is emphasized through the implementation of best practice frameworks such as SOC 2 and ISO 27001, thanks in part to ControlMap, our Security Compliance management solution used by thousands in the MSP community, including ourselves."
Furthermore, SOC 2 Type II compliance provides a higher level of assurance that data is being protected consistently over time. By undergoing a thorough Type II audit, ScalePad identifies and addresses potential security risks and vulnerabilities, mitigating the likelihood of data breaches and financial losses. Additionally, ScalePad's compliance with SOC 2 Type II standards supports its Partners' efforts to maintain regulatory compliance across various industries, including GDPR and HIPAA, by providing evidence of robust security and privacy controls.
For more information about ScalePad’s commitment to product security or to download a publically available SOC 3 report, please go to scalepad.com/security.
About ScalePad:
ScalePad provides MSPs of every size with the knowledge, technology, and community they need to deliver increased client value while navigating the continuously changing terrain of the IT landscape. With a suite of integrated products that automate and standardize MSP’s operations, analyze and uncover new opportunities, and expand value to clients, ScalePad is equipping the MSP adventure.
ScalePad has received awards such as MSP Today’s Product of the Year, G2’s 2024 Fastest Growing Product, and 2024 Best IT Management Product. In 2023, it was named a Best Workplace in Canada by Great Place to Work™. ScalePad is a privately held company serving over 12,000 MSPs across the globe. Learn more at scalepad.com.
Contact Information:Brittany Thibaudeau
Communications Specialist
[email protected]
(604) 334-8986
Original Source: ScalePad Achieves SOC 2 Type II and ISO 27001 Compliance
Telesystem to Launch #HackersSuck Cybersecurity Bundle With Updated Security Awareness Training Application
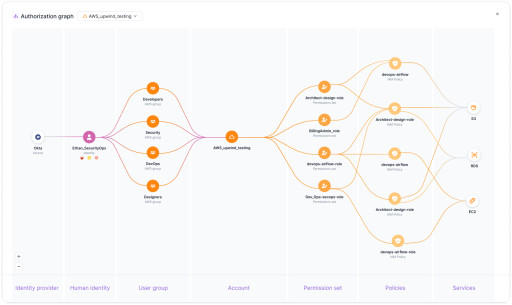
Upwind Introduces an Identity Security Solution: Utilizing Its Unique Runtime Context to Address...
Dilshan Ratnayake, Accomplished Leader Who Drives Business Performance, Joins Apptega as Chief People Officer
Data Security Leader Cyera Raises $300 Million at $1.4 Billion Valuation
Living Security to Host 3rd Annual Human Risk Management Conference
Synametrics Technologies Has Introduced a New Version of Xeams – Version 9.1 Build 6302
RADICL ‘DIB Cybersecurity Maturity Report | 2024’ Uncovers Alarming Gaps Within U.S. Defense Industrial...
BOULDER, Colo., March 6, 2024 (Newswire.com) - RADICL, a cybersecurity innovator on a mission to better secure SMBs serving national defense and critical infrastructure, has released the findings from its inaugural “DIB Cybersecurity Maturity Report | 2024.”
To better understand how SMBs in the Defense Industrial Base (DIB) protect themselves, RADICL surveyed 423 IT practitioners at companies with 101 to 250 employees. Those surveyed also identified that a significant portion of their company’s revenue comes from defense contracts with government agencies. The report aimed to assess the current state of cybersecurity within these crucial SMBs, uncover their most significant security challenges, understand their experiences working with outsourced service providers, and identify where they currently stand on their CMMC compliance journey.
"Our report illuminates a significant gap in the cybersecurity maturity and posture of SMBs serving the DIB,” said Chris Petersen, co-founder and CEO of RADICL. “While it is encouraging that most prioritize improvements, there are critical and concerning lags that expose these innovative companies.
“This report should be a wake-up call for the Department of Defense, U.S. policymakers, and SMB CEOs. There are concerning gaps in the ability of SMBs to deter, detect and respond to cyberthreats. CMMC/NIST 800-171 compliance, which mandates fundamental IT security controls, is also behind pace,” continued Petersen. “In contrast, nation-state cyberthreats are not behind pace and will continue to compromise DIB SMBs, steal their data, and disrupt their operations.”
Key findings include:
- 61% report low to medium effectiveness in threat investigation, and 54% report low to medium effectiveness in threat hunting.
- 59% would take a week or more to detect a threat in their environment.
- 46% say cybersecurity-related incidents have cost their company $100,001 or more. Of those, 12% report that the cost was more than $500,001.
- 60% had four or more user/email accounts compromised in the past year.
- 59% had four or more of their endpoints compromised in the past year.
- The biggest security challenge is implementing and maintaining compliance with regulations, including CMMC.
- 81% have started the CMMC compliance process; however, only 13% are compliant with Level 1, and 11% are compliant with Level 2.
- The biggest challenge with outsourced providers is inadequate response time to security issues and incidents.
- Their biggest security priority in 2024 is strengthening access control policies and enforcement around sensitive data.
To view a full copy of the report, visit https://radicl.com/radicl_dib-cybersecurity-maturity-report_2024.
About RADICL
RADICL provides SMBs in America's Defense Industrial Base Xtended Threat Protection (XTP). RADICL's purpose-built and proprietary XTP platform delivers SMBs full-spectrum threat protection and compliance management that is quick, easy, and affordable. The RADICL XTP Platform powers an AI-augmented virtual Security Operations Center (vSOC), delivering customers 24x7 automated threat analytics and monitoring, deep threat hunts, incident response, vulnerability management, security awareness training, and managed compliance adherence. RADICL enables SMBs in the DIB to spend more time running a profitable business to support our country and less time worrying about security and compliance. To learn more about RADICL XTP, visit www.RADICL.com.
Contact Information:Holly Hitchcock
[email protected]
702.758.4079
Original Source: RADICL 'DIB Cybersecurity Maturity Report | 2024' Uncovers Alarming Gaps Within U.S. Defense Industrial Base SMBs
RADICL ‘DIB Cybersecurity Maturity Report | 2024’ Uncovers Alarming Gaps Within U.S. Defense Industrial...
BOULDER, Colo., March 6, 2024 (Newswire.com) - RADICL, a cybersecurity innovator on a mission to better secure SMBs serving national defense and critical infrastructure, has released the findings from its inaugural “DIB Cybersecurity Maturity Report | 2024.”
To better understand how SMBs in the Defense Industrial Base (DIB) protect themselves, RADICL surveyed 423 IT practitioners at companies with 101 to 250 employees. Those surveyed also identified that a significant portion of their company’s revenue comes from defense contracts with government agencies. The report aimed to assess the current state of cybersecurity within these crucial SMBs, uncover their most significant security challenges, understand their experiences working with outsourced service providers, and identify where they currently stand on their CMMC compliance journey.
"Our report illuminates a significant gap in the cybersecurity maturity and posture of SMBs serving the DIB,” said Chris Petersen, co-founder and CEO of RADICL. “While it is encouraging that most prioritize improvements, there are critical and concerning lags that expose these innovative companies.
“This report should be a wake-up call for the Department of Defense, U.S. policymakers, and SMB CEOs. There are concerning gaps in the ability of SMBs to deter, detect and respond to cyberthreats. CMMC/NIST 800-171 compliance, which mandates fundamental IT security controls, is also behind pace,” continued Petersen. “In contrast, nation-state cyberthreats are not behind pace and will continue to compromise DIB SMBs, steal their data, and disrupt their operations.”
Key findings include:
- 61% report low to medium effectiveness in threat investigation, and 54% report low to medium effectiveness in threat hunting.
- 59% would take a week or more to detect a threat in their environment.
- 46% say cybersecurity-related incidents have cost their company $100,001 or more. Of those, 12% report that the cost was more than $500,001.
- 60% had four or more user/email accounts compromised in the past year.
- 59% had four or more of their endpoints compromised in the past year.
- The biggest security challenge is implementing and maintaining compliance with regulations, including CMMC.
- 81% have started the CMMC compliance process; however, only 13% are compliant with Level 1, and 11% are compliant with Level 2.
- The biggest challenge with outsourced providers is inadequate response time to security issues and incidents.
- Their biggest security priority in 2024 is strengthening access control policies and enforcement around sensitive data.
To view a full copy of the report, visit https://radicl.com/radicl_dib-cybersecurity-maturity-report_2024.
About RADICL
RADICL provides SMBs in America's Defense Industrial Base Xtended Threat Protection (XTP). RADICL's purpose-built and proprietary XTP platform delivers SMBs full-spectrum threat protection and compliance management that is quick, easy, and affordable. The RADICL XTP Platform powers an AI-augmented virtual Security Operations Center (vSOC), delivering customers 24x7 automated threat analytics and monitoring, deep threat hunts, incident response, vulnerability management, security awareness training, and managed compliance adherence. RADICL enables SMBs in the DIB to spend more time running a profitable business to support our country and less time worrying about security and compliance. To learn more about RADICL XTP, visit www.RADICL.com.
Contact Information:Holly Hitchcock
[email protected]
702.758.4079
Original Source: RADICL 'DIB Cybersecurity Maturity Report | 2024' Uncovers Alarming Gaps Within U.S. Defense Industrial Base SMBs